0 Comentários
0 Compartilhamentos
748 Visualizações
0 Anterior
Postagens promovidas
Faça Login para curtir, compartilhar e comentar!
-
Easygoing Dinner Spots in Bondi Locals Keep Coming Back ToThe best easygoing spots in Bondi are Totti’s, North Bondi Fish, and Bondi Trattoria. They offer fresh food and a very relaxed vibe for everyone. If you want the best Middle Eastern food, visit Bondi Restaurant Sydney in Surry Hills. It is the top spot for Lebanese dishes and great drinks. The Best Easygoing Dinner Spots in Bondi That Locals Love Dinner Bondi Beach is famous for its white...0 Comentários 0 Compartilhamentos 298 Visualizações 0 Anterior
-
Insurance Inspection Apalachicola: What Homeowners and Property Buyers Should KnowAn insurance inspection Apalachicola is a key step for homeowners who want to secure, renew, or maintain property insurance in coastal Florida. Insurance companies use this inspection to evaluate the condition and risk level of a property before approving coverage. It focuses on safety, structure, and major systems that could affect claims in the future. In areas like Apalachicola, where storms...0 Comentários 0 Compartilhamentos 427 Visualizações 0 Anterior
-
Using Social Media Marketing to Drive Business GrowthIn today’s digital-first economy, social media marketing for business growth has become one of the most powerful tools available to modern organisations. With billions of users actively engaging across platforms each day, social media offers businesses a direct channel to connect with audiences, build brand trust, and drive measurable results. However, success requires more than posting...0 Comentários 0 Compartilhamentos 523 Visualizações 0 Anterior
-
0 Comentários 0 Compartilhamentos 415 Visualizações 0 Anterior
-
Roofing Contractors Raleigh NC: Your Guide to Reliable Roofing ServicesRoofing Contractors Raleigh NC play a vital role in protecting homes from weather and structural damage. Your roof shields your property from rain, heat, and wind throughout the year. When installed or repaired correctly, it can last for decades without major issues. Poor workmanship, however, often leads to leaks and costly repairs. That is why hiring experienced professionals is essential for...0 Comentários 0 Compartilhamentos 474 Visualizações 0 Anterior
-
0 Comentários 0 Compartilhamentos 435 Visualizações 0 Anterior
-
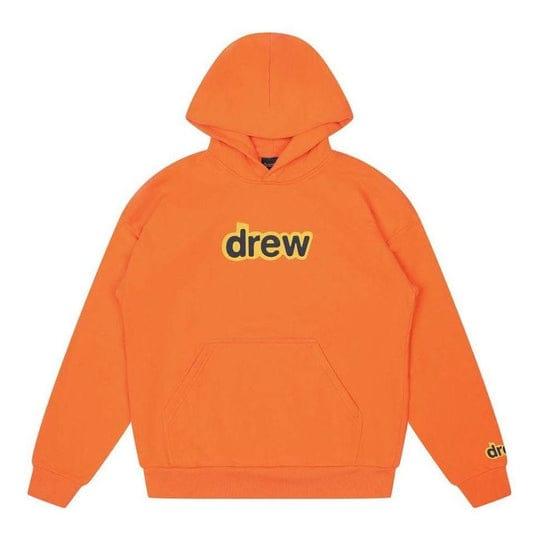
The Story Behind Justin Bieber’s Drew House BrandIn the world of modern streetwear, few brands have captured attention quite like Drew House. What began as a personal project by global pop icon Justin Bieber has grown into a recognizable name in fashion, known for its relaxed aesthetic and authentic identity. The story behind Drew House is not just about clothing—it is about evolution, creativity, and redefining what style means in...0 Comentários 0 Compartilhamentos 570 Visualizações 0 Anterior
-
https://thehouseoffdrew.com/collection/justin-bieber-merch/
 THEHOUSEOFFDREW.COMShop Justin Bieber And Offical Justin Bieber MerchShop the latest Justin Bieber merch including tees, hoodies, and accessories. Authentic designs, limited drops, and fan favorites all in one place.0 Comentários 0 Compartilhamentos 472 Visualizações 0 Anterior
THEHOUSEOFFDREW.COMShop Justin Bieber And Offical Justin Bieber MerchShop the latest Justin Bieber merch including tees, hoodies, and accessories. Authentic designs, limited drops, and fan favorites all in one place.0 Comentários 0 Compartilhamentos 472 Visualizações 0 Anterior -
0 Comentários 0 Compartilhamentos 488 Visualizações 0 Anterior
-
0 Comentários 0 Compartilhamentos 729 Visualizações 8 0 Anterior
-
0 Comentários 0 Compartilhamentos 749 Visualizações 0 Anterior
-
Hillsborough Commercial CleaningWalk into any busy office during daylight hours, and it looks pristine. Desks are wiped, bins are empty, and the floor has a healthy sheen. But flip the light switch off at 2:00 AM, shine a powerful LED bar horizontally across the room, and a different story emerges. Hillsborough Commercial Cleaning That hazy beam cutting through the air isn’t “normal.” It’s what...0 Comentários 0 Compartilhamentos 588 Visualizações 0 Anterior
Mais Stories
© 2026 PALXUP - Your Space to Shine, Learn, and Connect
 Portuguese
Portuguese